In this tutorial, you will learn how to crate your own free VPN server with free Open VPN, Dropbear SSH client, S tunnel and Squid Proxy. This VPN server created using free VPS provided by Google Cloud Platform free tier, but it works with any VPS server provider.
You can use this for TLS tunnel and HTTP injector apps to get secure internet connection. This is a Google Cloud VPN server that use a secure tunnel. You will never face security issues like in free VPN. Let’s go to the process. Don’t miss anything stay until end.
Autoscript include:
Services;
- Port OpenSSH 22,444
- Port Dropbear 80,143
- Port SSL 443
- Port Squid 8000,8080 (limit to IP SSH)
- Port UDPGW 7200
- badvpn : badvpn-udpgw port 7200
- OpenVPN : TCP 1194 & UDP 25000
- Nginx : 81
Script
- menu : displays a list of available commands
- usernew : create new SSH account
- trial : create a trial account
- hapus : delete SSH account
- cek : check user login
- member : check SSH members
- reboot : reboot VPS
- speedtest : speed test VPS
- info : display system information
- about : information about auto install script
- Other features
VPS AUTO REBOOT EVERY 12 HOURS 12 NIGHTS.
RUN INTO COMMANDS AFTER COMPLETE SCRIPT INSTALLATION.
Webmin : http://ExternalIP:10000/
Config Free OpenVPN TCP : http://ExternalIP/client-tcp.ovpn
Config Free OpenVPN UDP : http://ExternalIP/client-udp.ovpn
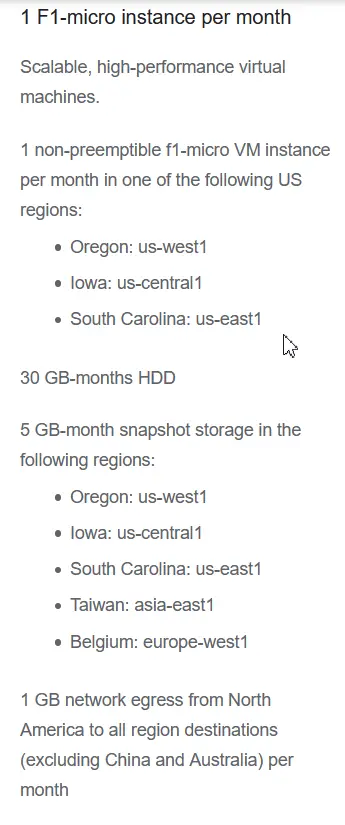
Setup Google Cloud VM Instance
First, sign up to Google Cloud Platform using your Google account. In the dashboard, under “compute engine” click “VM instance”. Then click “create” button to setup new virtual machine.
Enter name of the VM instance what ever you like. Chose a region and zone that include in google cloud platform free tier. Then select machine type f1 micro under N1 series. Click “change” button to select a boot disk.
You have to select Ubuntu 18.04 LTS as the OS and the version. Leave other settings default and click “select” button. Under firewall, tick mark both allow HTTP and HTTPS traffic. After finishing the setup, click “create” button to deploy the VPS.
Setup VPC Network
You have to get a static IP address for the instance. In the main menu, select “external IP address” under “VPC network”. Change the IP type to “Static”. The Static IP address is not change during restart the server.
Now, you have to set a firewall rule to allows VPN server ports. In the VM instances page, click “setup firewall rule” at the bottom of the page. Then, click “crate firewall rule” button at the top of the page. Enter a name for the rule and change the target to “all instance in the network”. If you want you can choose a specific target. Enter this source IP range to allow all ranges of IP addresses.
IP Range: 0.0.0.0/0
Under protocols and ports, select allow all to open all port of the VPS. After all, click “create” button at the bottom. Now, VPS setup is over. Let’s see how to create a VPN server.
Setup Free VPN Server
Click “SSH” button of the VM instance to get terminal window. To get root access, enter the command.
sudo -sYou have to add a user to the server. Use the following command and don’t forget to Replace the user name. Here, enters a password to user and verify it by retyping. You can fill this detail or skip by pressing “enter” button.
sudo adduser usernameNow, give root access to new user using this command. Replace username that you entered.
usermod -aG sudo usernameUse exit command to log out in root user.
exitLog in to the new user, entering the password.
su usernameUse this command to get root access and enter the user password.
sudo -sNow, we finished the adding a new user and gave the root access. Download the VPN server script using this command.
wget http://evira.us/ubi18.shUse this line for make sure the script is executable.
chmod +x ubi18.shNow execute the script using this command. This takes some time to get ready your server. Please be peasant.
./ubi18.shOk, now VPN server is ready. You can see the details of the server here. Just copy and keep the all the details here in safe place.
Following are the features of this script:
- OpenSSH, ports: 22, 444
- Dropbear, ports: 80, 143
- SSL, port: 443
- Squid3, port: 8000, 8080 (limit to IP VPS)
- Badvpn: badvpn-udpgw port 7200
- Webmin
- OpenVPN: TCP 1194 and UDP 25000
- Menu script: displays a list of available commands
- Usernew script: create SSH and OpenVPN accounts
- Trial script: create SSH and OpenVPN trial accounts
- Delete script: delete SSH and OpenVPN accounts
- Check script: check user login
- Script member: check the list of SSH and OpenVPN members
- Script speedtest: VPS speedtest
- Info script: displays system information
- Script about: information about the auto install script
- VPS auto reboots every 12 at night
Add a New VPN User
Before adding a user, reboot the VPN server using this command. It may cause to disconnection of the terminal window for a few moments. Try to connect it again.
rebootAfter re connection, get root access to add a new VPN user.
sudo -sYou can type “menu” to get all VPN server commands.
menuUse new user command and add the asking credentials. You have to enter user name, password and expiration time of the account. Then, copy the all details of the user.
Now, all set at the server side. Let’s see how to configure client side.
Connect to HTTP Injector
I try to connect it using HTTP injector a popular app. If the app is not in your mobile, use Google Play Store to install it. Open the app and change the tunnel type to TLS SSL Stunnel. In the main menu, select SSH settings.
Try to fill all the details here using your server information. enter external IP address as SSH host name and SSH port as 443. Enter your relevant VPN username and password that we entered in previous step. Untick enable proxy port.
If you want you can use Custom SNI but it is not necessary. After finishing the setup, click “start” button. You can see here it successfully connected to your own server. Let’s check the IP address to verify it.
You can see the server IP address and internet service provider. It’s Google Cloud Platform. No worry anymore about your data security. You are totally safe here.
Webmin Admin Access
You can access your VPN server using Webmin IP address that was given by the server information. login in using administrator user we initially created.
http://IPVPS:10000Get Premium VPN or Proxy Server
You can get cheap premium proxy or VPN server that more stable and secured. Check these providers and select what is the best one for you.



Can You Update ubi18.sh file please
ok
ok
OK I will update the script
this method will work with any cloud service
before adding any commands add this commands ————————————————–
sudo apt-get update && apt install -y accountsservice acl acpid adduser amd64-microcode apparmor apport apport-symptoms apt apt-utils at base-files base-passwd bash bash-completion bc bcache-tools bind9-host bsdmainutils bsdutils btrfs-progs btrfs-tools busybox-initramfs busybox-static byobu bzip2 ca-certificates cloud-guest-utils cloud-init cloud-initramfs-copymods cloud-initramfs-dyn-netconf command-not-found command-not-found-data console-setup console-setup-linux coreutils cpio crda cron cryptsetup cryptsetup-bin curl dash dbus debconf debconf-i18n debianutils diffutils dirmngr distro-info distro-info-data dmeventd dmidecode dmsetup dns-root-data dnsmasq-base dnsutils dosfstools dpkg e2fsprogs eatmydata ebtables ed eject ethtool fdisk file findutils fonts-ubuntu-console friendly-recovery ftp fuse gawk gcc-8-base gdisk geoip-database gettext-base gir1.2-glib-2.0 git git-man gnupg gnupg-l10n gnupg-utils gpg gpg-agent gpg-wks-client gpg-wks-server gpgconf gpgsm gpgv grep groff-base grub-common grub-gfxpayload-lists grub-legacy-ec2 grub-pc grub-pc-bin grub2-common gzip haveged hdparm hostname htop info init init-system-helpers initramfs-tools initramfs-tools-bin initramfs-tools-core install-info intel-microcode iotop iproute2 iptables iputils-ping iputils-tracepath irqbalance isc-dhcp-client isc-dhcp-common iso-codes iucode-tool iw kbd keyboard-configuration klibc-utils kmod krb5-locales landscape-common language-selector-common less libaccountsservice0 libacl1 libapparmor1 libapt-inst2.0 libapt-pkg5.0 libargon2-0 libasn1-8-heimdal libassuan0 libatm1 libattr1 libaudit-common libaudit1 libbind9-160 libblkid1 libbsd0 libbz2-1.0 libc-bin libc6 libcap-ng0 libcap2 libcap2-bin libcom-err2 libcryptsetup12 libcurl3-gnutls libcurl4 libdb5.3 libdbus-1-3 libdbus-glib-1-2 libdebconfclient0 libdevmapper-event1.02.1 libdevmapper1.02.1 libdns-export1100 libdns1100 libdrm-common libdrm2 libdumbnet1 libeatmydata1 libedit2 libelf1 liberror-perl libestr0 libevent-2.1-6 libexpat1 libext2fs2 libfastjson4 libfdisk1 libffi6 libfreetype6 libfribidi0 libfuse2 libgcc1 libgcrypt20 libgdbm-compat4 libgdbm5 libgeoip1 libgirepository-1.0-1 libglib2.0-0 libglib2.0-data libgmp10 libgnutls30 libgpg-error0 libgpm2 libgssapi-krb5-2 libgssapi3-heimdal libhavege1 libhcrypto4-heimdal libheimbase1-heimdal libheimntlm0-heimdal libhogweed4 libhx509-5-heimdal libicu60 libidn11 libidn2-0 libip4tc0 libip6tc0 libiptc0 libirs160 libisc-export169 libisc169 libisccc160 libisccfg160 libisns0 libjson-c3 libk5crypto3 libkeyutils1 libklibc libkmod2 libkrb5-26-heimdal libkrb5-3 libkrb5support0 libksba8 libldap-2.4-2 libldap-common liblocale-gettext-perl liblvm2app2.2 liblvm2cmd2.02 liblwres160 liblxc-common liblxc1 liblz4-1 liblzma5 liblzo2-2 libmagic-mgc libmagic1 libmnl0 libmount1 libmpdec2 libmpfr6 libmspack0 libncurses5 libncursesw5 libnetfilter-conntrack3 libnetplan0 libnettle6 libnewt0.52 libnfnetlink0 libnghttp2-14 libnih1 libnl-3-200 libnl-genl-3-200 libnpth0 libnss-systemd libntfs-3g88 libnuma1 libp11-kit0 libpam-cap libpam-modules libpam-modules-bin libpam-runtime libpam-systemd libpam0g libparted2 libpcap0.8 libpci3 libpcre3 libperl5.26 libpipeline1 libplymouth4 libpng16-16 libpolkit-agent-1-0 libpolkit-backend-1-0 libpolkit-gobject-1-0 libpopt0 libprocps6 libpsl5 libpython3-stdlib libpython3.6 libpython3.6-minimal libpython3.6-stdlib libreadline5 libreadline7 libroken18-heimdal librtmp1 libsasl2-2 libsasl2-modules libsasl2-modules-db libseccomp2 libselinux1 libsemanage-common libsemanage1 libsensors4 libsepol1 libsigsegv2 libslang2 libsmartcols1 libsqlite3-0 libss2 libssl1.0.0 libssl1.1 libstdc++6 libsystemd0 libtasn1-6 libtext-charwidth-perl libtext-iconv-perl libtext-wrapi18n-perl libtinfo5 libudev1 libunistring2 libunwind8 libusb-1.0-0 libutempter0 libuuid1 libuv1 libwind0-heimdal libwrap0 libx11-6 libx11-data libxau6 libxcb1 libxdmcp6 libxext6 libxml2 libxmlsec1 libxmlsec1-openssl libxmuu1 libxslt1.1 libxtables12 libyaml-0-2 libzstd1 linux-base linux-firmware linux-generic linux-headers-4.15.0-156 linux-headers-4.15.0-156-generic linux-headers-generic linux-image-4.15.0-156-generic linux-image-generic linux-modules-4.15.0-156-generic linux-modules-extra-4.15.0-156-generic locales login logrotate lsb-base lsb-release lshw lsof ltrace lvm2 lxcfs lxd lxd-client man-db manpages mawk mdadm mime-support mlocate motd-news-config mount mtr-tiny multiarch-support nano ncurses-base ncurses-bin ncurses-term net-tools netbase netcat-openbsd netplan.io networkd-dispatcher nplan ntfs-3g open-iscsi open-vm-tools openssh-client openssh-server openssh-sftp-server openssl os-prober overlayroot parted passwd pastebinit patch pciutils perl perl-base perl-modules-5.26 pinentry-curses plymouth plymouth-theme-ubuntu-text policykit-1 pollinate popularity-contest powermgmt-base procps psmisc publicsuffix python-apt-common python3 python3-apport python3-apt python3-asn1crypto python3-attr python3-automat python3-blinker python3-certifi python3-cffi-backend python3-chardet python3-click python3-colorama python3-commandnotfound python3-configobj python3-constantly python3-cryptography python3-dbus python3-debconf python3-debian python3-distro-info python3-distupgrade python3-gdbm python3-gi python3-httplib2 python3-hyperlink python3-idna python3-incremental python3-jinja2 python3-json-pointer python3-jsonpatch python3-jsonschema python3-jwt python3-markupsafe python3-minimal python3-netifaces python3-newt python3-oauthlib python3-openssl python3-pam python3-pexpect python3-pkg-resources python3-problem-report python3-ptyprocess python3-pyasn1 python3-pyasn1-modules python3-requests python3-requests-unixsocket python3-serial python3-service-identity python3-six python3-software-properties python3-systemd python3-twisted python3-twisted-bin python3-update-manager python3-urllib3 python3-yaml python3-zope.interface python3.6 python3.6-minimal readline-common rsync rsyslog run-one screen sed sensible-utils shared-mime-info snapd software-properties-common sosreport squashfs-tools ssh-import-id strace sudo sysstat systemd systemd-sysv sysvinit-utils tar tcpdump telnet thermald time tmux tzdata ubuntu-advantage-tools ubuntu-keyring ubuntu-minimal ubuntu-release-upgrader-core ubuntu-server ubuntu-standard ucf udev ufw uidmap unattended-upgrades update-manager-core update-notifier-common ureadahead usbutils util-linux uuid-runtime vim vim-common vim-runtime vim-tiny wget whiptail whois wireless-regdb xauth xdelta3 xdg-user-dirs xfsprogs xkb-data xxd xz-utils zerofree zlib1g libc6 libffi6 libgcc1 liblz4-1 liblzo2-2 libmariadb3 libpcap0.8 libssl1.1 libstdc++6 zlib1g bridge-utils net-tools libsasl2-2 iproute2 sqlite3 libsqlite3-0 iptables python3-pkg-resources python3-migrate python3-sqlalchemy python3-mysqldb python3-ldap3
dear friend, Can you help me to find out use these installation method with other cloud service providers such as aws,linode,azure,digitalocean etc. I tried with aws but it did not work
After creating new user you should add this commands
1. apt update
2. apt install -y libc6 libffi6 libgcc1 liblz4-1 liblzo2-2 libmariadb3 libpcap0.8 libssl1.1 libstdc++6 zlib1g bridge-utils net-tools libsasl2-2 iproute2 sqlite3 libsqlite3-0 iptables python3-pkg-resources python3-migrate python3-sqlalchemy python3-mysqldb python3-ldap3
This should be work for it check whether you follow the all steps including port opening. If not work, I will update it in future.
This should be work for it check whether you follow the all steps including port opening. I will update it in future.
Can help me to install this on aws ubuntu server.I tried these methords but it didn’t work
This should be work for it check whether you follow the all steps including port opening. If not work, I will update it in future.
How can I remove users from my VPN server?
How can I limit client account logins? please help me.
Please follow to info menu
i can’t login to webmin. I also can’t connect ssh + httpinjector. Please help me. Sir
I think your google cloud account trial is over. Now they limited the trail period. Your computer instant is paused. You have to enable payment account for continue running of the instant. It will charge monthly fee for the network usage. I suggests to use Oracle cloud free tier.
any guide here?, currently trying here with oracle (currently use an SNI bug host with a public ssh server) would be awesome to router via the cloud instance, tried running the script but get the error: Exec format error
what instance are you used for that. A1 Arm or AMD one?